TÜV TRUST IT TÜV AUSTRIA GMBH
Kick-off: Cybersecurity-Center an der TU Wien
Spannender Austausch bei Podiumsdiskussion
Bei der Eröffnungsveranstaltung des fakultätsübergreifenden Zentrums der Technischen Universität Wien am 18.4.2024 kamen Forscher_innen, Praktiker_innen und Entscheidungsträger_innen zusammen, um die Zusammenarbeit und den Wissensaustausch zu fördern und so den Herausforderungen der Cybersicherheit auf lokaler als auch auf globaler Ebene zu begegnen.
Bei der Podiumsdiskussion betonten die Teilnehmenden – darunter Andreas Köberl (TÜV TRUST IT TÜV AUSTRIA GMBH) – unter anderem die Rolle von Universitäten bei der Kenntnisvermittlung über Cybersicherheit an Industrie und öffentlichen Sektor. Eine interdisziplinäre Strategie soll Verständnis- und Anwendungslücken schließen und die Widerstandsfähigkeit gegen Cyberbedrohungen stärken.

Brandschutztag in der Burg Perchtoldsdorf
Künstliche Intelligenz im Brandschutz:
Brand aus, bevor Brand da
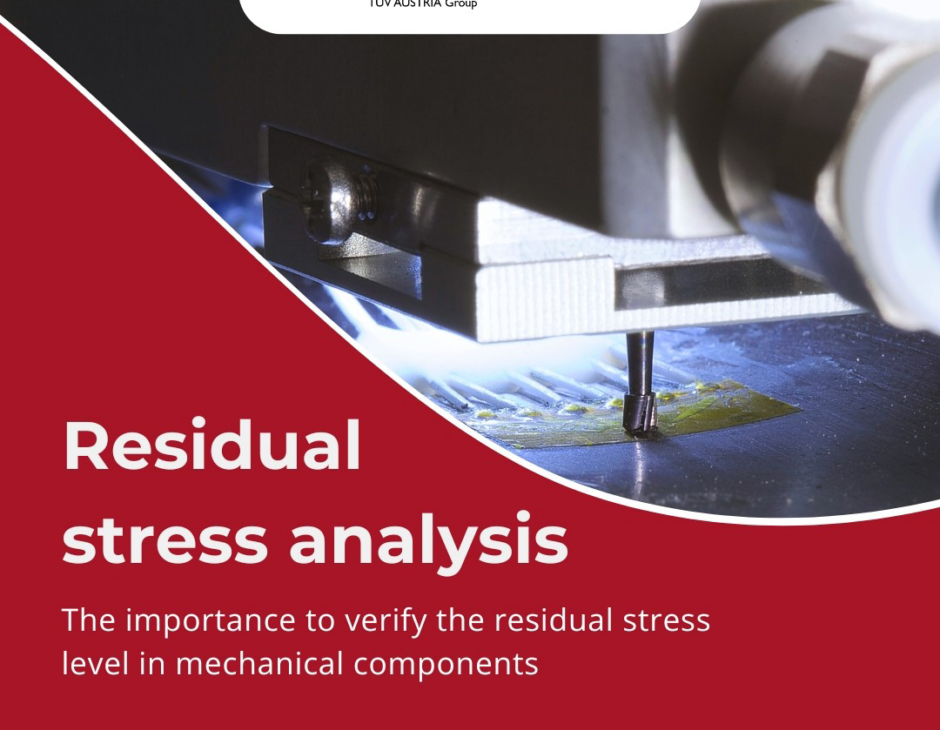
Messtechnik
Eigenspannungsanalyse in mechanischen Komponenten
Mit modernster Messtechnik
SINT Technology, ein Unternehmen der TÜV AUSTRIA Group, führt Überprüfungen des Eigenspannungsniveaus in mechanischen Komponenten mit modernster Messtechnik durch.

Spielplatzsicherheit
Leitfaden „Spielen, aber SICHER!“
TÜV AUSTRIA unterstützt bei Spielplatz-Praxisseminaren
Das Praxisseminar „Spielen, aber SICHER!“ klärt über die richtige Wartung und Instandhaltung von Spielplätzen und Schulhöfen auf. Mit Herrn Robert Terp vom TÜV AUSTRIA steht der NÖ Familienland GmbH nun schon seit vielen Jahren ein Experte in Sachen Sicherheit auf Spielplätzen für dieses Praxisseminar als Vortragender zur Seite.
Quelle: gutentag.news | Guten Tag Österreich

Expertentag
CSR & Nachhaltigkeit aus allen Blickwinkeln
Geballte Vielfalt beim TÜV AUSTRIA Expertentag im Mai!

Nachhaltigkeit
TÜV AUSTRIA Hellas bei den Green Brand Awards 2024 prämiert:
Gold- und Silberauszeichnung für Nachhaltigkeitsengagement





Unser
TÜV AUSTRIA Showcase
Unsere Lösungen der Woche
-
ICT Industrielle Computertomographie
Branche: Industrie
-
Ankaufs- und Verkaufstest für Einfamilienhäuser und Gewerbeimmobilien
Branche: Bau & Real Estate
-
Umweltsimulation
Branche: Industrie
Unterstützung benötigt?
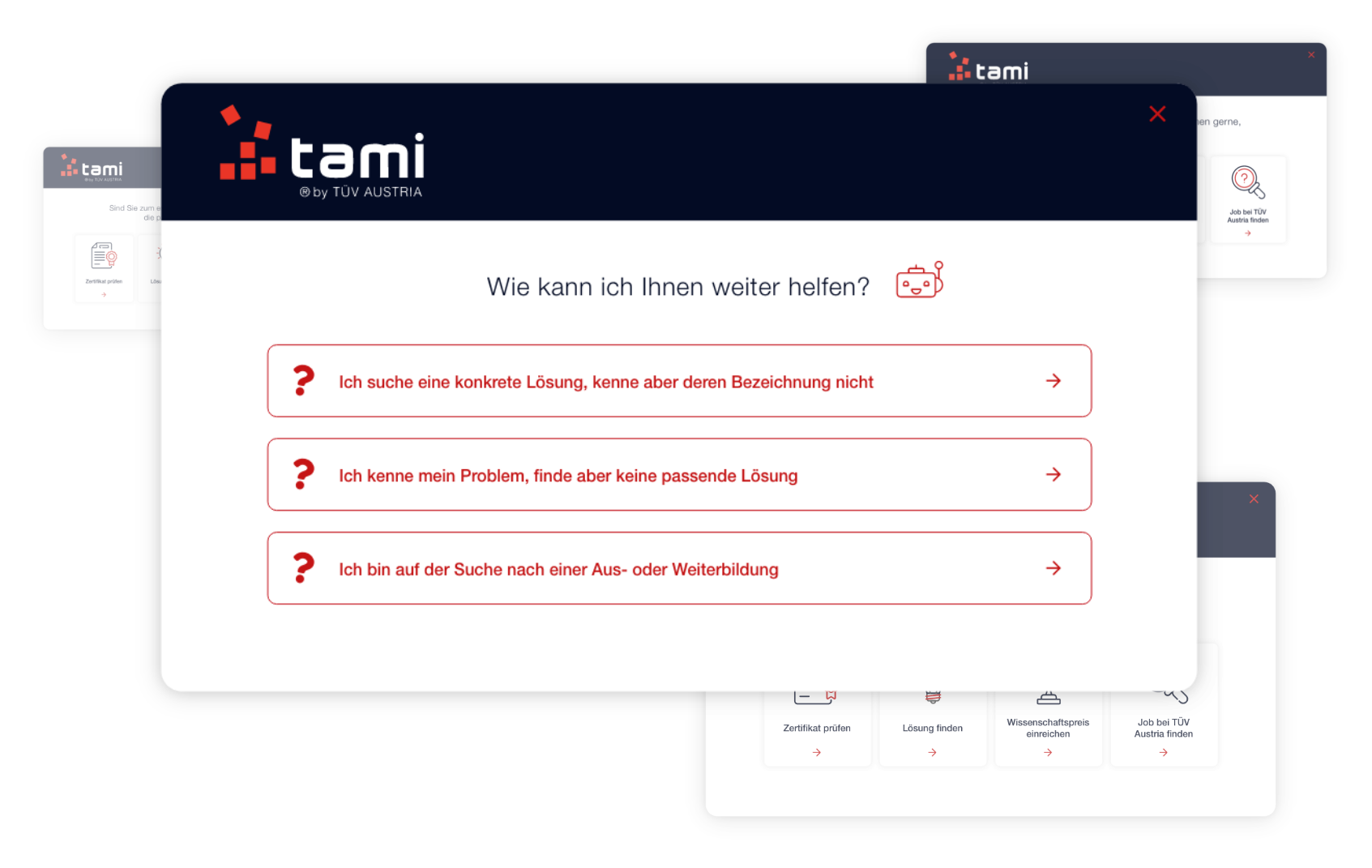
tami ist der digitaler Wegbereiter und hilft unseren Kund:innen bei ihren Anliegen.
tami ist der TÜV AUSTRIA Wegbereiter für Unternehmen in der digitalisierten Marktlandschaft. In Österreich und auf der ganzen Welt – hosted in Austria. tami zeigt den richtigen Weg – auch bei der Suche auf unserer Website. Frag’ tami@tuv.at
´
Unsere Leistungen
überzeugen
Mehr über unsere Lösungen erfahren -
Audit & Certification TÜV AUSTRIA zertifiziert Managementsysteme, Personen und Produkte.
Entdecken -
Fachverlag Der TÜV AUSTRIA Fachverlag bietet ein umfangreiches Sortiment an Fachbüchern, Skripten und Dokumentationshilfen.
Entdecken -
Guidance Die TÜV AUSTRIA Expert_innen begleiten Sie gerne rund um das Thema “Sicherheit”.
Entdecken -
Testing & Inspection TÜV AUSTRIA agiert als unabhängiges Prüf- und Inspektionsunternehmen.
Entdecken -
Training Die TÜV AUSTRIA Akademie bietet mehr als 2.400 praxisnahe Kurse für jedes Weiterbildungsziel.
Entdecken

Gründe, warum Sie uns vertrauen können
-
+ 1
Mitarbeiter:innen beschäftigt TÜV AUSTRIA
-
+ 1
Aus- & Weiterbildungs-teilnehmer:innen jährlich
-
+ 1
Arbeitsstunden für Sicherheit & Qualität
-
1 t
CO2 Einsparungen in Österreich