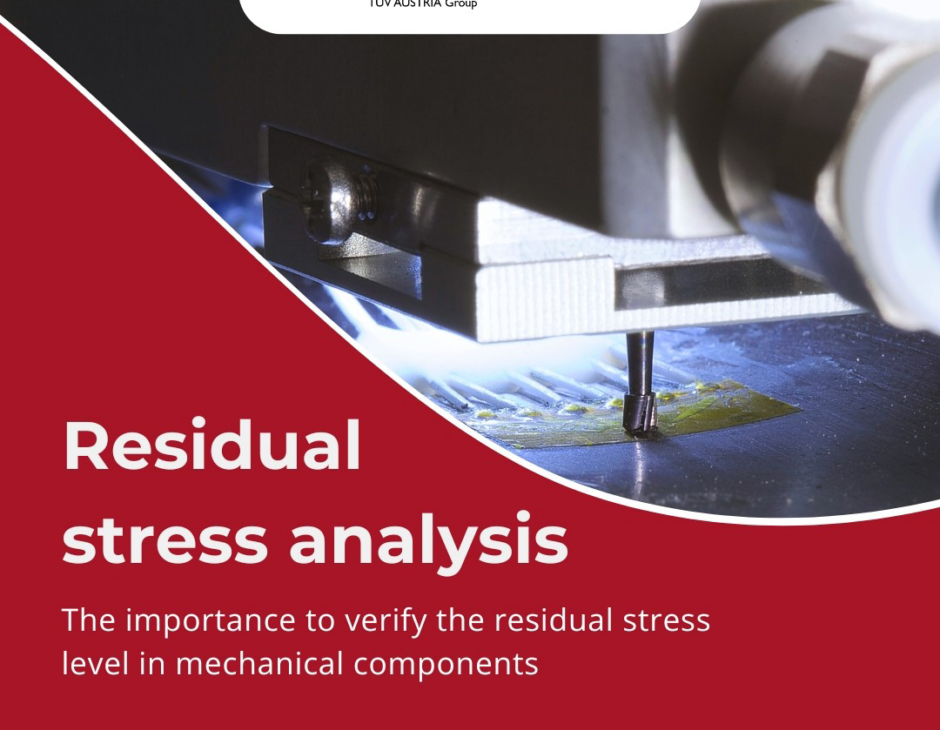
Messtechnik
Eigenspannungsanalyse in mechanischen Komponenten
Mit modernster Messtechnik
SINT Technology, ein Unternehmen der TÜV AUSTRIA Group, führt Überprüfungen des Eigenspannungsniveaus in mechanischen Komponenten mit modernster Messtechnik durch.

Spielplatzsicherheit
Leitfaden „Spielen, aber SICHER!“
TÜV AUSTRIA unterstützt bei Spielplatz-Praxisseminaren
Das Praxisseminar „Spielen, aber SICHER!“ klärt über die richtige Wartung und Instandhaltung von Spielplätzen und Schulhöfen auf. Mit Herrn Robert Terp vom TÜV AUSTRIA steht der NÖ Familienland GmbH nun schon seit vielen Jahren ein Experte in Sachen Sicherheit auf Spielplätzen für dieses Praxisseminar als Vortragender zur Seite.
Quelle: gutentag.news | Guten Tag Österreich

Expertentag
CSR & Nachhaltigkeit aus allen Blickwinkeln
Geballte Vielfalt beim TÜV AUSTRIA Expertentag im Mai!

Nachhaltigkeit
TÜV AUSTRIA Hellas bei den Green Brand Awards 2024 prämiert:
Gold- und Silberauszeichnung für Nachhaltigkeitsengagement

Photovoltaik
Lehrgang schafft neue Fachkräfte
So wird Zukunft gestaltet: PV-Lehrgang der TÜV AUSTRIA Akademie und dem Bundesverband Photovoltaic Austria überarbeitet

FAQ
Neue ISO-Anforderung:
Klimawandel wird in alle Managementsystemstandards aufgenommen
Am 22. Februar 2024 veröffentlichten IAF und die Internationale Organisation für Normung (ISO) ein gemeinsames Kommuniqué, um die Veröffentlichung von Klimaschutzänderungen zu neuen und bestehenden ISO-Managementsystemnormen zur Unterstützung der ISO-London-Erklärung hervorzuheben. Ziel ist es, sicherzustellen, dass die Organisation neben allen anderen Themen auch Fragen des Klimawandels im Kontext der Wirksamkeit des Managementsystems berücksichtigt. TÜV AUSTRIA hat die FAQ rund um die Neuerung für Sie zusammengefasst.





Unser
TÜV AUSTRIA Showcase
Unsere Lösungen der Woche
-
Ankaufs- und Verkaufstest für Einfamilienhäuser und Gewerbeimmobilien
Branche: Bau & Real Estate
-
Umweltsimulation
Branche: Industrie
-
ICT Industrielle Computertomographie
Branche: Industrie
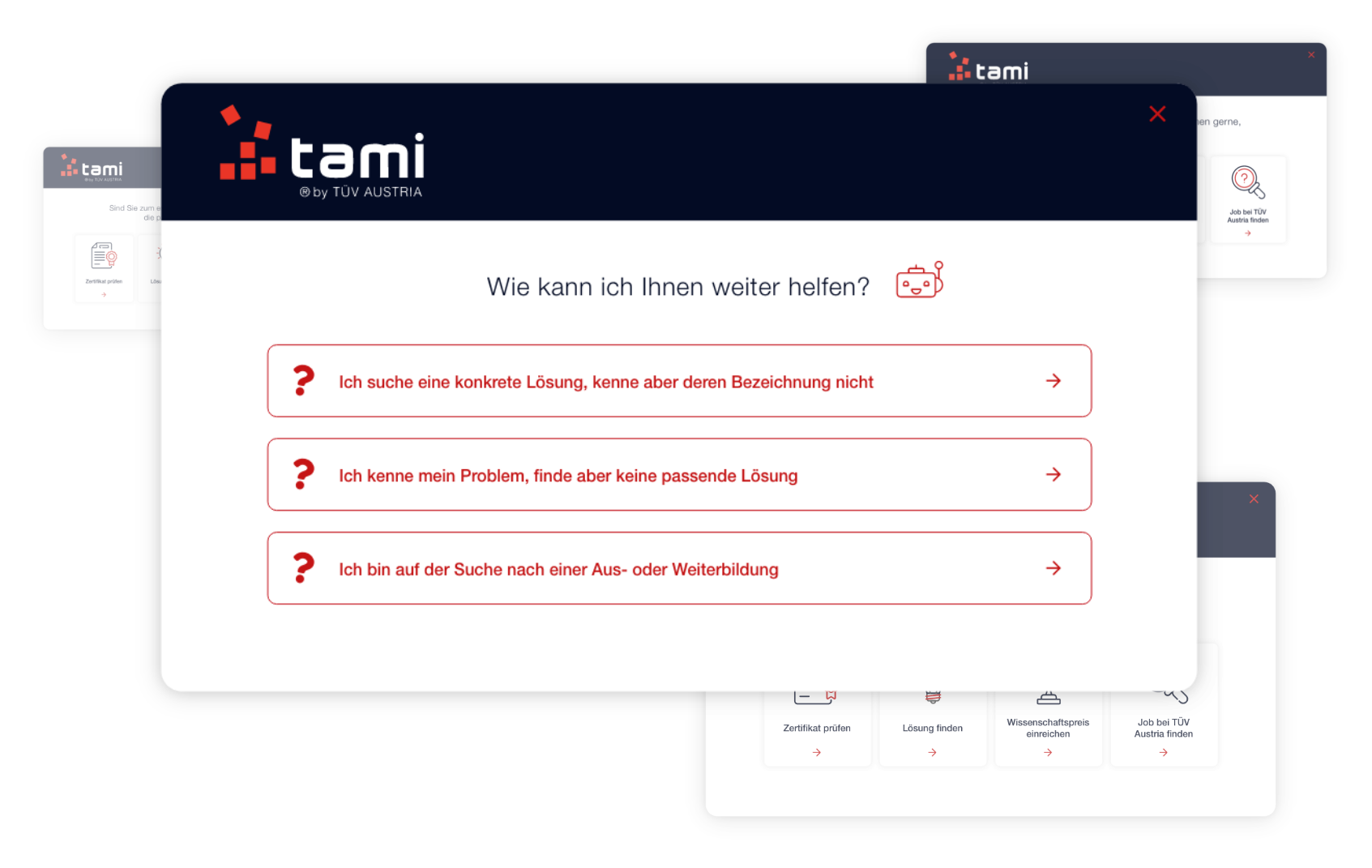
Unterstützung benötigt?
tami ist der digitaler Wegbereiter und hilft unseren Kund:innen bei ihren Anliegen.
tami ist der TÜV AUSTRIA Wegbereiter für Unternehmen in der digitalisierten Marktlandschaft. In Österreich und auf der ganzen Welt – hosted in Austria. tami zeigt den richtigen Weg – auch bei der Suche auf unserer Website. Frag’ tami@tuv.at
´
Unsere Leistungen
überzeugen
Mehr über unsere Lösungen erfahren -
Audit & Certification TÜV AUSTRIA zertifiziert Managementsysteme, Personen und Produkte.
Entdecken -
Fachverlag Der TÜV AUSTRIA Fachverlag bietet ein umfangreiches Sortiment an Fachbüchern, Skripten und Dokumentationshilfen.
Entdecken -
Guidance Die TÜV AUSTRIA Expert_innen begleiten Sie gerne rund um das Thema “Sicherheit”.
Entdecken -
Testing & Inspection TÜV AUSTRIA agiert als unabhängiges Prüf- und Inspektionsunternehmen.
Entdecken -
Training Die TÜV AUSTRIA Akademie bietet mehr als 2.400 praxisnahe Kurse für jedes Weiterbildungsziel.
Entdecken

Gründe, warum Sie uns vertrauen können
-
+ 1
Arbeitsstunden für Sicherheit & Qualität
-
+ 1
Aus- & Weiterbildungs-teilnehmer:innen jährlich
-
+ 1
Mitarbeiter:innen beschäftigt TÜV AUSTRIA
-
1 t
CO2 Einsparungen in Österreich